Hackers in China Attacked The Times for Last 4 Months
Chinese hackers have been persistently attacking The New York Times over the last 4 months, infiltrating its computer systems and getting passwords for its reporters and other employees.
The Times and Computer Security experts, after surreptitiously tracking the intruders, have erected better defenses to block them. They have expelled the attackers and kept them from further breaking-in.
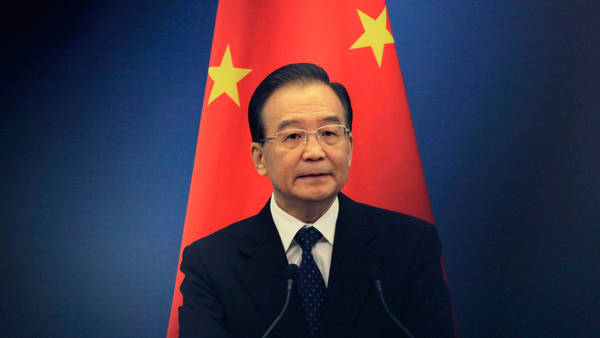
The timing of the hacking coincided with the report published on 25th October about accumulation of wealth worth several billion dollars by the relatives of Wen Jiabao, China’s Prime Minister.
Evidence of hacking
Mandiant, Security experts hired by The Times gathered digital evidences breaching The Times Network. The hackers broke into the e-mail account of David Barboza, the Shanghai Bureau Chief, who wrote the reports about the accumulation of wealth and the e-mail account of Jim Yardley, South Asia Bureau Chief located in India. The hackers seemed to have cloaked their operation by breaking through different routes – US Universities.
Modus Operandi
The attackers first installed malware (malicious software) which enabled access to any computer in The Times Network. This malware was identified by the computer security experts as a specific strain associated with computer attacks originating in China. They also found evidence that the hackers broke into the computers of 53 employees. However, no customer data was stolen.
China’s Response
China’s Ministry of National Defense registered that Chinese Laws prohibit any acton including hacking that damages Internet Security. They added that it was unprofessional and baseless to accuse the launch of cyber attacks without solid proof.
Precedent
Last year, the Bloomberg News Agency was targeted by the Chinese hackers for report on the wealth accumulated by Xi Jimping, China’s Vice president at that time. A spokesman for Bloomberg that hackers had made attempts, however, without any data loss on the computers.
Probable Motive
It is assumed that the hackers began operations in 2008. These attacks suggest that the aim is far-reaching spying campaign at an expanding set of targets including corporations, government agencies, activist groups, and media organizations in the United States. This is an effort trying to control China’s public image, domestically and abroad. They aimed to intimidate their sources’ contacts and to anticipate stories that might damage the reputation of the Chinese leaders.
Follow-up
The Times notified and voluntarily briefed the Federal Bureau of Investigation on the attack. Monitoring on the attackers continued. The hackers seemed to operate during the day time (in Beijing) and seemed to have intermittent breaks of 2 weeks. The passwords of all computers were changed and additional security was wrapped. This has ensured that no further ‘break-in’s’ however, constant alert and monitoring is persistently followed. Close watch and studies have commenced, analyzing what holds and what may happen as the next steps. Thus, cyber attacks have turned out to be truly international in perspective, carrying mind-boggling intriguesas to the future.
